In 2025, a single telecommunications company operating a single AI spam-detection system flagged over 9.6 million suspicious text messages in just two months. Globally, another platform with 500 million users identified and blocked 68 billion spam calls in a single year. These numbers, staggering as they are, represent only a fraction of the fraud epidemic reshaping how people communicate.
Spam calls and fraudulent calls have ceased to be isolated nuisances. They are now the visible symptom of a vast, largely invisible infrastructure where stolen data, automated dialing systems, cloud telephony, and weak regulation converge to create one of the world’s most persistent digital threats.
Key Findings:
- Nigeria leads Africa in spam intensity: 51% of all unknown calls received by Nigerians in 2025 were identified as spam or fraudulent, placing the country 8th globally.
- Global fraud losses reached record levels: Americans reported $15.9 billion in fraud losses in 2025 alone, a 27% increase from the prior year. When accounting for underreporting, total losses may exceed $195.9 billion annually.
- Loan app harassment is weaponized: Over 11,000 complaints were filed in Nigeria between 2021 and 2023 regarding harassment and data abuse by digital lenders. The problem persists despite regulatory action.
- Automated systems dominate call volumes: In the hardest-hit markets, more than 70% of unknown calls are now machine-generated, a trend expected to intensify.
- AI-enabled fraud is exploding: Voice cloning fraud rose 680% in the past year. Deepfake vishing attacks surged by 1,633% in Q1 2025 compared to Q4 2024. Global AI-enabled fraud losses are projected to reach $40 billion by 2027.
- Data breaches fuel the machine: Over 119,000 data breaches were recorded in Nigeria in Q1 2025 alone, exposing millions of phone numbers, bank details, and personal identifiers used by fraudsters.
- SIM card vulnerabilities are systemic: Recycled SIM cards, pre-registered numbers, and database leaks create a perpetual supply of phone numbers for fraud operations. Innocent consumers are arrested based on crimes committed by previous SIM holders.
The core thesis of this report is simple: spam calls are not a technology problem requiring only better filters. They are a business problem, a regulatory problem, and an infrastructure problem. Every fraudulent call that reaches a victim’s phone represents a chain of exploitation involving data brokers, VoIP providers, automated dialers, compromised telecom employees, and organized fraud networks operating from multiple continents.
This report investigates that chain, identifies the actors profiting from it, and examines what happens when the default response to an incoming call becomes silence.
Chapter 1: The global explosion of SpamCall
The Scale of the Crisis
The numbers are almost incomprehensible in scale. In 2025, Truecaller, a caller identification platform with over 500 million monthly active users, detected and blocked 68 billion spam and fraud calls globally. This represents not the total number of spam calls made, but only those identified by users of a single application. The actual global volume is orders of magnitude higher.
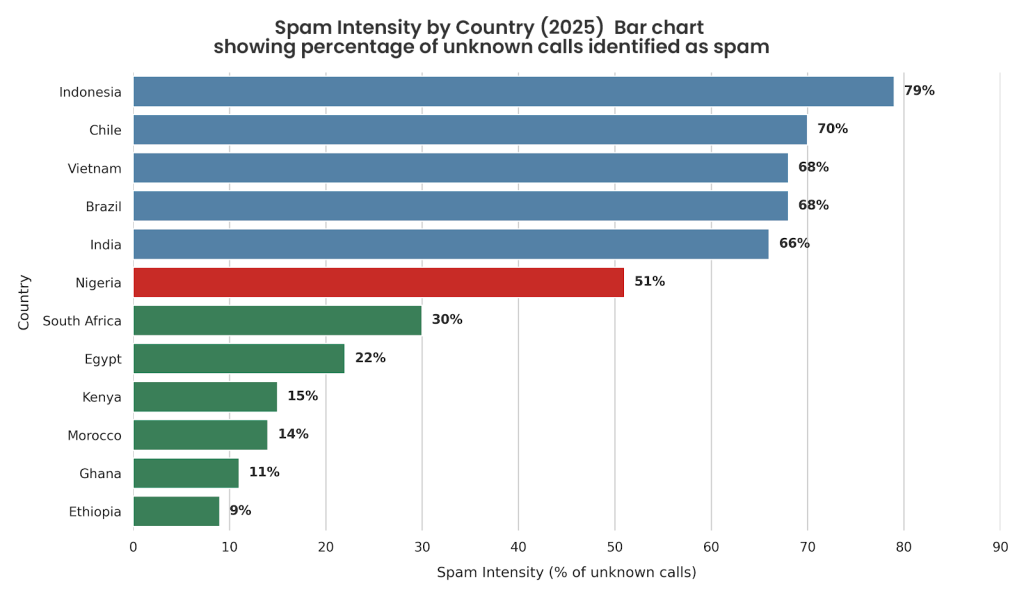
Indonesia, with 79% of unknown calls flagged as spam or fraud, has become the global epicenter of the spam call crisis. Chile follows at 70%, a dramatic increase from 51% just six months earlier. Vietnam, Brazil, and India round out the top five, all with spam intensities exceeding 65%.
In Africa, the pattern is distinct but no less alarming. Nigeria, with 51% of unknown calls identified as spam or fraudulent, leads the continent and ranks 8th globally. What distinguishes Nigeria from other high-spam markets is not just volume but composition: while Indonesia and Mexico are dominated by financial services impersonation scams, Nigeria’s ecosystem is shaped by telecom and operator-linked outreach, which accounts for 35% of all spam calls, the highest concentration of any African market.
South Africa records 30% spam intensity, Kenya 15%, Ghana 11%, and Ethiopia 9%, suggesting that the problem intensifies with population size, mobile penetration, and inadequate regulatory infrastructure.
Financial Impact: The True Cost
The financial devastation is both personal and systemic. In the United States alone, consumers reported losing $15.9 billion to fraud in 2025, a 27% increase from $12.5 billion in 2024. However, law enforcement agencies estimate that only 2-6.7% of fraud victims report their losses, suggesting that actual losses could exceed $195.9 billion annually when accounting for underreporting.
Investment scams accounted for the largest share of losses at $7.9 billion in 2025, followed by imposter scams at nearly $3 billion. Cryptocurrency fraud reached $9.3 billion in the United States alone, representing a 66% increase from the prior year.
The cost extends beyond consumer losses. Businesses worldwide lost 7.7% of their annual revenue on average to fraud, an estimated $534 billion across the 1,200 business leaders surveyed. In the United States, the figure is even more severe: 9.8% of corporate revenue, or an estimated $114 billion among surveyed companies alone.
Behavioral Shift: When Trust Breaks Down
The psychological cost may ultimately exceed the financial one. As spam saturation increases, the default human response is avoidance. When most unknown calls are spam, people stop answering.
In Nigeria, this shift has profound consequences. Doctors, schools, delivery services, financial institutions, and legitimate businesses now compete for attention on devices that experience has trained users to ignore. Missed calls become missed appointments, delayed diagnoses, dropped revenue, and customer relationships that quietly fade away.
This represents a fundamental breakdown in how voice communication functions. The phone call, once a symbol of immediacy and trust, has become a filtered and suspect medium. As one Truecaller CEO stated: “In some countries, most unknown calls are now spam. That is a fundamental breakdown in how communication works.”
Who Is Hit Hardest
Older adults bear the greatest financial burden. In the United States, people age 60 and older reported $7.7 billion in losses to fraud in 2025, a 60% increase from the prior year. Job seekers, loan-dependent populations, and individuals with lower digital literacy are also disproportionately targeted.
In Nigeria and Africa, the vulnerable populations are even larger: youth seeking employment, informal traders, small business owners relying on voice communication, and the 75% of the continent’s population still without reliable internet access and therefore dependent on SMS and voice calls as primary communication channels.
Chapter 2: How the Spam Call Machine Works
The Technical Stack
Every spam call that reaches a victim’s phone is the output of a complex technical infrastructure. Understanding this infrastructure is critical to understanding why enforcement has failed and why the problem accelerates.
Data Acquisition: The chain begins with phone numbers. Fraudsters acquire these through multiple channels:
- Leaked databases from data breaches
- SIM registration records sold by compromised telecom employees
- Contact lists harvested by loan apps and e-commerce sites
- Phone numbers purchased from data brokers
- Public directories and online forms
- Recycled SIM cards containing previous owners’ financial records
In Nigeria, the scale of data breaches is staggering. Over 119,000 data breaches were recorded in Q1 2025 alone. One investigation found that personal data, including National Identification Numbers, Bank Verification Numbers, and photographs, could be purchased online for as little as N100 (less than one cent USD). A website called XpressVerify received 567,990 visits in February 2024 and 188,360 visits in April 2024, with each query selling sensitive personal data.
Contact Databases: Once acquired, phone numbers are compiled into massive contact databases. These are often tiered by value: high-value targets (business owners, account holders with substantial balances) command premium prices, while bulk lists of consumers are commoditized.
Auto-Dialers and Robocall Software: The actual calling is handled by automated systems. These range from sophisticated cloud-based platforms to open-source PBX systems like Asterisk. An auto-dialer can make thousands of simultaneous calls, with calls distributed across time zones to maximize the probability of reaching live targets during business hours.
The software typically integrates with Interactive Voice Response (IVR) systems, the automated systems that play pre-recorded messages or connect callers to human agents. A single auto-dialer running on commodity hardware can process millions of calls per day.
VoIP and SIP Routing: International calls are routed through Voice-over-IP (VoIP) networks using the Session Initiation Protocol (SIP). This is where the economics of spam calls become apparent. A legitimate international call from Nigeria to the United States might cost $0.10-$0.20 per minute through conventional telecom infrastructure. The same call routed through a VoIP provider costs $0.01-$0.03.
For fraudsters, this cost advantage is enormous. A campaign targeting 1 million numbers can be executed for $10,000-$30,000 using VoIP, compared to hundreds of thousands using traditional infrastructure. This economic reality means that even if only 0.1% of targets respond with a payment, the campaign is profitable.
SIMBox Fraud: A particularly insidious variant is SIMBox fraud, where international VoIP calls are intercepted and rerouted through physical SIM cards in the destination country. This bypasses telecom operator revenue entirely and allows fraudsters to appear as local callers, a critical element of social engineering. A SIMBox contains multiple SIM cards and routes VoIP traffic through them, generating local call termination charges while avoiding international fees.
Caller ID Spoofing: The system displays a spoofed caller ID, often the phone number of a government agency, bank, or telecom operator. This is technically trivial to execute over VoIP networks, which allow arbitrary caller ID values. SMS spoofing is even easier.
AI-Generated Voices: The most recent evolution involves AI-generated voices that can clone a specific person’s voice from a brief audio sample. A 3-second recording is sufficient to generate a convincing synthetic voice capable of conducting entire conversations. This technology has crossed what researchers call the “indistinguishable threshold”, the point at which human listeners cannot reliably detect that a voice is synthetic.
The Full Lifecycle
A typical spam call operation follows this sequence:
- Target Selection: Fraudsters purchase a contact list or harvest numbers from public sources. Lists are segmented by geography, age, income level, or employment status.
- Campaign Setup: A robo-dialing campaign is configured with a pre-recorded message, target numbers, timing parameters, and geographic distribution across time zones. The IVR is configured to classify responses (answered, busy, answering machine, human) and route only live human responses to sales agents.
- Initial Contact: The auto-dialer places millions of simultaneous calls. Calls display a spoofed caller ID that appears legitimate. Each call attempts to trigger an emotional response, urgency, fear, greed, or obligation.
- Live Agent Handoff: If the target responds positively, the call is transferred to a live agent, often working from a call center thousands of miles away. The agent uses social engineering techniques tailored to the target’s vulnerability.
- Payment Collection: The victim is instructed to transfer money, purchase gift cards, install software, or provide access to financial accounts. Payment methods are chosen to maximize irreversibility: wire transfers, cryptocurrency, gift cards, and peer-to-peer payment apps all leave minimal paper trail.
- Money Laundering: Fraudulently obtained funds are rapidly laundered through money mules, cryptocurrency mixers, and offshore accounts. Studies show that fewer than 5% of funds obtained through sophisticated fraud schemes are ever recovered.
The entire operation is automated at scale, with artificial intelligence used to optimize call timing, detect network blocks, and generate more convincing synthetic voices. The barrier to entry is now measured in hundreds of dollars and a basic understanding of VoIP and auto-dialer software.
Chapter 3: The Data Economy Behind the Spam Calls
The Supply Chain of Personal Information
Phone numbers are only valuable if they can be connected to vulnerable individuals. The data economy that supplies this connection is vast, fragmented, and almost entirely unregulated outside of a few jurisdictions.
Data Breaches as Source Material: The foundation is breaches. In Nigeria alone, over 119,000 data breaches were recorded in Q1 2025. These breaches expose phone numbers alongside names, addresses, bank account details, National Identification Numbers (NINs), and even biometric data. The breaches span government agencies, private companies, healthcare systems, and financial institutions.
One investigation found that personal data from government identity systems could be queried for as little as N100 per record. Journalists were able to purchase NINs and Bank Verification Numbers of multiple other journalists by simply providing a phone number.
Loan App Data Harvesting: Nigeria’s digital lending ecosystem has become a primary vector for data harvesting. Loan apps request access to contact lists, call logs, photos, and location data. Once installed, many apps silently harvest and upload this data to remote servers. When borrowers default, the apps use this contact data for harassment, messaging family members, employers, and friends with threats and public shaming.
Between 2021 and 2023, the Federal Competition and Consumer Protection Commission received over 11,000 complaints about harassment, data abuse, and unethical recovery tactics by digital lenders. This number excludes unreported cases, which experts estimate to be significantly larger.
E-Commerce and Service Sites: Every time a consumer provides a phone number to an online retailer, sign up for a service, or enters a sweepstakes, that data is captured. Some of these sites are operated by legitimate companies that maintain reasonable security. Many are not. Data is frequently sold to data brokers or exposed in breaches.
SIM Registration Leaks: Mobile network operators maintain vast databases linking SIM cards to National Identification Numbers and personal details. These databases have been periodically breached or accessed through compromised employees. A single employee with database access can export millions of records for sale to criminal organizations.
Public Sources and Data Brokers: Phone numbers appear in public directories, social media profiles, business listings, and government websites. Data brokers aggregate this public information and sell it in bulk to anyone willing to pay. A contact list of 1 million Nigerian phone numbers can be purchased for $500-$2,000.
The Monetization Pipeline
Once acquired, personal data becomes monetized through multiple channels:
Direct Sales: Data brokers sell contact lists to fraudsters, marketers, and spam operators. Pricing varies by segmentation and freshness: a list of verified business owners costs more than a random sample of consumers.
Targeting Services: Sophisticated fraudsters purchase not just phone numbers but psychographic profiles—data indicating which individuals are vulnerable to specific scams. Someone who recently searched for loan information is more likely to respond to a loan scam. Someone who recently searched for investment opportunities is more likely to respond to an investment fraud.
Verification Services: Once a fraudster has a list of phone numbers, they can verify which numbers are active, which are associated with banks, and which are linked to specific individuals. Verification services that appear to have legitimate purposes (identity verification, fraud prevention) are instead weaponized for targeting.
The Regulatory Response (and Its Limitations)
Nigeria’s Federal Competition and Consumer Protection Commission issued groundbreaking regulations in 2025—the Digital, Electronic, Online, or Non-Traditional Consumer Lending Regulations (DEON)—that explicitly ban unauthorized contact harvesting, public shaming, and harassment. The regulations came into effect July 21, 2025.
However, enforcement remains slow and reactive. For every loan app delisted, new ones appear with cloned interfaces and slightly different names. By October 2025, 434 digital lenders had obtained full approval, 36 held conditional approval, but 103 remained under regulatory watch. Over 47 apps had been delisted, yet the ecosystem continued to grow.
The core problem is systemic: as long as harvestable data remains accessible and valuable, fraudsters will find ways to harvest it. Without simultaneous improvements to data protection, device security, and law enforcement, regulation alone cannot stem the flow.
Chapter 4: Loan Apps and The Harassment Economy in Nigeria
The Scale of the Problem
Nigeria’s digital lending ecosystem serves a critical function: it provides credit to millions excluded from traditional banking. Yet this same ecosystem has been weaponized into an instrument of mass harassment and harassment-enabled fraud.
The numbers are staggering. Over 200 mobile loan apps operate in Nigeria, with only a fraction properly regulated. Between 2021 and 2023, the FCCPC received 11,000+ complaints. In 2025, the Nigeria Data Protection Commission reported handling an average of nearly three new loan-shark privacy complaints daily.
These complaints describe systematic abuse:
- Contact List Harassment: Apps silently harvest entire contact lists and use them for public shaming. Borrowers report receiving messages from family members, employers, and friends containing fabricated stories, claims that they are criminals, HIV-positive, or deceased.
- Debt Shaming: One borrower reported receiving messages labeling him as a “criminal” sent to his employer. A woman was publicly shamed on social media with her photograph, leading to job loss.
- Predatory Interest Rates: A borrower who needs ₦20,000 and repays within 10 days pays ₦5,000 in interest, a 250% annualized rate. A ₦50,000 loan at a 7-day term with late fees can cost over ₦65,000 to repay.
- Financial Entrapment: Borrowers take a loan to cover an emergency, repay it, then take another for a different emergency. Within months, the pattern becomes habitual. The app begins extending terms and increasing loan amounts without explicit consent, a violation of the new regulations.
Case Studies
Case 1 – The Employment Trap: A 23-year-old recent graduate in Lagos borrowed ₦20,000 from a loan app to supplement her income while searching for permanent employment. She repaid within the agreed term. The app then automatically extended her a larger loan. When she failed to repay on time due to a family illness, the app sent messages to her contacts claiming she was a “fraud” and a “criminal.” Her employer saw one such message. She was terminated for “character concerns.” Six months of employment prospects were damaged due to information she never authorized to be shared.
Case 2 – The Recycled SIM Problem: A man in Ibadan purchased a new SIM card. Unknown to him, the number had been previously used by a loan app to harass its customers. The prior holder had defaulted. The new SIM owner then began receiving calls from people claiming he owed them money. He eventually discovered the source and reported it, but only after weeks of anxiety. The old debt was not his, but the damage to his reputation was real.
Case 3 – The Public Shaming Campaign: A woman in Port Harcourt defaulted on a ₦15,000 loan. The app sent explicit images to her family members claiming she had engaged in sex work to obtain the money. The images were fabricated. Her family relations were damaged. She eventually proved the deception, but legal recourse was limited.
Regulatory Response
The FCCPC’s 2025 Digital Lending Regulations represent the most comprehensive framework yet:
- Mandatory registration with the FCCPC
- Transparent disclosure of terms, interest rates, and fees
- Ban on automatic lending without explicit consent
- Explicit prohibition of contact list access and harassment
- Penalties up to ₦100 million or 1% of annual turnover for violations
- Disqualification of directors for up to 5 years
In practice, enforcement faces obstacles:
- Scale: Hundreds of apps operate in the shadows, accessible only through direct downloads outside official app stores. Each delisting leads to rebrand and relaunch.
- International Dimensions: Many loan apps are operated from other countries. Enforcement requires international cooperation rarely available.
- Speed of Fraud vs. Speed of Regulation: A fraudulent app can be created, acquire users, extract value, and disappear faster than regulators can investigate and prosecute.
- Complicit Infrastructure: Apps use phone numbers spoofed to appear as coming from legitimate telecom operators, creating confusion for users and evading network-level blocking.
The larger issue is that loan apps exist in a market failure. Traditional banks exclude millions due to lack of collateral, credit history, or formal employment. Digital apps fill this gap but do so without the safety guardrails of regulated banking. The choice faced by policymakers is not between perfect and imperfect lending, but between imperfect lending and no lending at all.
Chapter 5: 419 Goes Automated
The Evolution of Advance-Fee Fraud
Advance-fee fraud, the so-called “Nigerian 419” scam, originated as a manual operation conducted by individual fraudsters sending emails and making phone calls. A victim would be contacted with a story: a wealthy individual needed help transferring funds out of a country, a lottery had been won, an inheritance was available, or a business opportunity required capital. All required the victim to pay a small upfront fee or provide bank details.
The manual operation was labor-intensive, had a low success rate, and generated limited total revenue. Modern automation has industrialized this model to a degree that earlier fraudsters could not have imagined.
Industrial-Scale Fraud
In 2025, the typical fraud operation follows this pattern:
Phase 1 – Targeting at Scale: Auto-dialers place millions of calls using spoofed government agency numbers. The IVR plays a prerecorded message about a loan, grant, prize, or legal action. Targets who show interest are routed to human agents.
Phase 2 – Social Engineering: Human agents use a script tailored to the target’s apparent vulnerability. An unemployed person receives a job offer. A struggling small business owner receives an investment opportunity. An elderly person receives news of a distant relative’s inheritance. Each story is customized to trigger an emotional response.
Phase 3 – Trust Building: The agent asks for personal information, creates fake documents, and builds rapport. This phase can last days or weeks. The victim is shown fake bank transfers, fake winning notifications, and fake business plans—all designed to build confidence.
Phase 4 – Extraction: Once trust is established, the victim is asked to pay a fee: visa fees for an international job, processing fees for a loan, legal fees for inheritance claim, or shipping fees for a prize. The fee is small relative to the promised benefit—typically $100-$1,000.
Phase 5 – Escalation: If the victim pays the initial fee, the fraudster introduces complications. A customs fee is required. A tax is due. An insurance payment is needed. Each complication requires another payment. Some victims pay tens of thousands before abandoning the scheme.
The Role of AI and Automation
Modern fraud operations layer automation on top of manual social engineering:
- Voice Cloning: AI can clone a voice using a brief audio sample, allowing fraudsters to conduct calls with synthesized voices that sound human. This reduces the need for live agents and increases call volume.
- Script Generation: Large language models generate customized scripts for each target, tailoring the story to apparent vulnerabilities gleaned from social media or data profiles.
- Multi-Channel Coordination: Fraud campaigns now integrate SMS, WhatsApp, voice calls, and email. A victim might receive a text message directing them to a WhatsApp chat, which directs them to a website, which directs them to a voice call. This creates multiple touchpoints and makes blocking difficult.
- Deepfake Video: The most sophisticated operations now use deepfake video technology to create fake video calls with convincing executives, government officials, or lottery representatives. The technology is now indistinguishable from authentic video to most observers.
Scale and Revenue
The scale of modern fraud operations is difficult to overstate. A single campaign targeting 10 million phone numbers costs less than $5,000 to execute. If 0.01% of targets engage and 10% of those pay an average of $200, the campaign generates $200,000 in revenue against a $5,000 cost.
Industry data suggests that average loss per fraud victim is now $500-$10,000, with high-value targets (business owners, retirees, high-net-worth individuals) losing significantly more. Some victims have reported cumulative losses exceeding $1 million spread across multiple frauds.
The total global revenue from fraud is estimated in the billions of dollars annually. Much of this flows through unregulated jurisdictions, making enforcement nearly impossible.
Chapter 6: The Business Infastructure Enabling the Industry
Legitimate Technologies, Illegitimate Uses
The infrastructure enabling spam calls and fraud consists largely of legitimate technologies designed for legal purposes. Understanding this infrastructure reveals why the problem is so difficult to solve and why technology alone cannot address it.
Cloud Telephony Platforms: Companies like Twilio, Vonage, and Nexmo provide APIs that allow developers to build communication applications. These platforms are used by legitimate businesses to send SMS alerts, automated appointment reminders, and two-factor authentication codes.
However, the same platforms can be exploited for fraud. A criminal can register an account using stolen identity information, load a list of phone numbers, and launch a campaign targeting millions. The platform’s terms of service prohibit this use, but enforcement is challenging at scale.
A single developer account can be used to send millions of messages per day before detection. When an account is shut down, the fraudster simply opens another using different stolen credentials. The economic calculation remains favorable: even if 90% of accounts are eventually detected, the remaining 10% generate sufficient revenue to offset losses.
Contact Center Software: Platforms like Genesys, NICE CX, and CISCO Webex Contact Center are designed to route incoming calls to agents and manage customer interactions. These platforms are legitimate tools for businesses.
Yet they are also the backbone of fraud call centers. A contact center operator can purchase these platforms, configure them to receive inbound calls from auto-dialers, and route calls to human agents. The software provides call recording, agent scripting, call quality monitoring—all features designed to improve legitimate customer service but equally useful for fraud operations.
Open-Source PBX Systems: Asterisk, a free and open-source Private Branch Exchange (PBX) system, provides complete telephony functionality. A PBX is the system that routes calls within a business. Asterisk is used by thousands of legitimate organizations to manage their internal communications.
Asterisk also enables fraud. A criminal can install Asterisk on a cheap server, configure it to receive VoIP calls from auto-dialers, and route them to live agents. The open-source nature means that source code can be modified to evade detection or add spoofing capabilities. Multiple Asterisk installations worldwide are known to be operated exclusively for fraud.
VoIP Providers: Services like 3CX, Jitsi, and others provide VoIP calling over the internet. These services have legitimate uses but are also weaponized for fraud. Some VoIP providers have minimal authentication and little-to-no fraud monitoring.
The challenge for these platforms is that they face a fundamental tradeoff: better security reduces ease of use and increases friction, discouraging legitimate users from adopting the service. Looser security increases user adoption but enables fraud. Economic incentives favor loose security, especially if fraud costs are externalized to users rather than borne by the platform.
Data Brokers and Information Trafficking
Dozens of companies worldwide operate as data brokers—buying and selling personal information legally or illegally. In the United States, this is partially regulated. In Nigeria and most of Africa, there is virtually no regulation.
Data brokers aggregate information from public records, online databases, social media, and breaches. They then sell this information in bulk to anyone willing to pay. A contact list of 1 million Nigerian phone numbers costs $500-$2,000. Segmented lists (by age, income, employment status) cost more.
Some data brokers operate quasi-legally, claiming that all data is from public sources or that consent was obtained. Others operate entirely in the shadows, selling stolen data on dark web marketplaces.
The Tension Between Innovation and Misuse
The fundamental challenge is that the same infrastructure enabling legitimate communication services also enables fraud. Twilio’s platform enables both legitimate SMS reminders and fraud campaigns. Asterisk enables both legitimate business telephony and fraud operations.
Technology companies face a misaligned incentive structure:
- Innovation drives adoption: Companies that make services easy to use and cheap to deploy gain market share.
- Ease of use enables misuse: The same ease that makes a platform attractive to legitimate users makes it attractive to fraudsters.
- Abuse costs are externalized: When fraud occurs, the cost falls on victims and law enforcement, not on the platform. The platform company receives its fees regardless.
- Enforcement is expensive: Detecting and preventing fraud at scale requires significant investment in monitoring, investigation, and compliance. Companies face pressure to minimize these costs.
The result is an infrastructure where fraud prevention is often an afterthought. Platforms implement minimal monitoring and investigation, shut down accounts only after large-scale misuse, and rarely cooperate with law enforcement.
Chapter 7: Human Impact
The Lived Experience of Spam Saturation
The financial losses, while massive, capture only part of the impact. The psychological, social, and health consequences are equally significant.
For Consumers: When most unknown calls are spam, people stop answering their phones. This creates cascading consequences:
- Job seekers miss calls from employers
- Patients miss appointment reminders, leading to missed medical care
- Parents miss school calls about emergencies
- Delivery services cannot reach customers, leading to failed deliveries and returned packages
- Financial institutions cannot reach account holders to report fraud or critical updates
The result is a digital broken windows effect: as trust erodes, the functionality of the phone as a communication device degrades. People begin using alternative channels (WhatsApp, email, apps), but these require Internet connectivity unavailable to rural populations and low-income users.
The elderly are disproportionately affected. Many older adults remain phone-dependent due to limited digital literacy or accessibility needs. The rise of spam means they are simultaneously vulnerable to fraud and isolated from legitimate contact.
For Small Businesses: Micro and small enterprises in Nigeria and Africa depend on voice communication for customer contact, supplier coordination, and payment processing. High spam saturation reduces the effectiveness of legitimate business calls. A small business struggling to reach customers faces a diminishing return on communication investment.
Psychological and Social Impact: Fraud victims report feelings of shame, violated trust, and hypervigilance. Some victims become socially isolated after experiencing public shaming through loan app harassment. Relationships are damaged when family members learn of fraudulent claims made in the victim’s name.
The elderly are particularly susceptible to the psychological impact. Deepfake voice scams in which a victim hears what sounds like their grandchild in distress have led to significant psychological trauma even in cases where the victim did not send money.
Healthcare Impacts: Rural clinics and hospitals in Nigeria often rely on phone calls to reach patients for appointment reminders, test results, or medication updates. High spam saturation makes these calls less effective. Patients miss critical health information.
One study found that increased spam saturation correlates with lower rates of medical appointment adherence, particularly among older adults who rely on phone calls for health maintenance.
Financial Impact Across Segments
Older Adults: Americans age 60+ reported $7.7 billion in losses to fraud in 2025—a 60% increase from the prior year. This represents losses that often consume life savings and retirement funds. Recovery is often impossible.
Job Seekers and Unemployed: Job scams increased 300% between 2020 and 2024. Unemployment increases vulnerability; desperate individuals are more likely to engage with suspicious offers.
Small Business Owners: In Nigeria, small business owners are targeted with fake loan offers, fake supplier quotes, and fake payment processing services. A single fraud can represent months of business income.
Loan-Dependent Populations: The irony is sharp: people who most need access to credit are most vulnerable to fraud. Loan apps and loan scams proliferate in the same communities, making it difficult to distinguish legitimate from fraudulent operators.
Chapter 8: Nigeria and Africa as a High-Risk Markets
Why Africa Is Vulnerable
Nigeria ranks 8th globally in spam intensity, the highest in Africa. This positioning is not accidental but rather reflects structural conditions that make the region particularly attractive to fraudsters and particularly difficult for defenders.
Rapid Smartphone Adoption Without Digital Literacy: Africa has experienced explosive growth in smartphone penetration. Nigeria’s mobile connections have grown to over 200 million. However, digital literacy has not kept pace. Many first-time smartphone users lack experience distinguishing legitimate from fraudulent communications.
Weak Regulatory Enforcement: Regulation exists but enforcement is limited by capacity, resources, and corruption. A regulator investigating 10,000 loan app fraud complaints faces a resource constraint that a regulator in the US or Europe with dedicated task forces and automated tools does not face.
Limited Law Enforcement Capacity: Cybercrime units in Nigerian law enforcement exist but are small relative to the scale of the problem. Investigating a single fraud case can consume weeks of detective work. With limited staff, only the most serious cases receive attention.
International Jurisdictional Challenges: Fraud operators are often located in different countries than victims. A Nigerian victim defrauded by someone operating from Ghana, India, or Southeast Asia faces a cross-border investigation challenge that law enforcement is often unable to resolve.
High Youth Unemployment: With limited formal employment opportunities, some youth turn to fraud. Nigeria has a large population of young, tech-savvy individuals facing unemployment. The barrier to entry to fraud—requiring only a computer and VoIP access—is lower than the barrier to legitimate employment.
Data Protection Infrastructure Gaps: While Nigeria has a Data Protection Commission and is implementing the Nigeria Data Protection Act, enforcement remains nascent. Data breaches occur regularly with limited consequences for responsible parties.
SIM Registration Leaks: The link between SIM cards and national identity numbers (NINs) means that SIM registration databases are targets for theft and resale. Once stolen, this data enables sophisticated targeted fraud.
Informal Financial Systems: Many Nigerians use informal money transfer systems like Payer, Opay, and others that are faster but less regulated than banks. These systems are targets for fraud and have weaker identity verification than traditional banking.
The Mobile Economy as Risk Vector
Paradoxically, the very infrastructure that enables financial inclusion also enables fraud. Mobile money platforms allow unbanked populations to participate in the digital economy. Yet the same platforms lack the security infrastructure of traditional banking.
In Nigeria, mobile money transactions in 2024 totaled trillions of naira. These transactions are increasingly targets for fraud. A fraudster who can convince a mobile money user to send funds has achieved irreversible fund transfer with minimal paper trail.
The GSMA’s Mobile Economy Africa 2025 report notes that the mobile sector contributed $220 billion to Africa’s economy in 2024. Yet nearly 75% of the continent remains offline, and of those online, many use inadequately secured platforms.
Comparative Risk Analysis
Nigeria’s 51% spam intensity is not unique in global context—Indonesia’s 79% is higher. Yet Nigeria’s structural vulnerabilities are greater than Indonesia’s, making the threat more consequential:
- Lower GDP per capita: Nigeria’s lower income levels mean that fraud losses represent a larger percentage of household income and are harder to recover from.
- Limited social safety net: Unlike developed countries with unemployment insurance and disaster relief programs, Nigeria’s social safety net is minimal. Fraud losses can be catastrophic.
- Higher dependence on voice communication: Rural areas and lower-income populations are more voice-dependent than email or app-dependent, increasing exposure to voice fraud.
- Larger youth population: Nigeria’s median age is 18 years old. A large population of young, tech-savvy but economically vulnerable individuals is an ideal target for fraud recruitment.
Chapter 9: How Truecaller Became a Defensive Layer
The Role of Third-Party Identification
Truecaller, a Swedish-founded caller identification platform, has become the primary defense against spam and fraud calls for hundreds of millions of users. The company operates on a simple principle: if enough users identify a call as spam, the system can identify subsequent calls from the same number as likely spam.
By March 2026, Truecaller had crossed 500 million monthly active users, with more than 150 million users outside India. The Middle East and Africa region crossed 100 million users in late 2025, making Africa one of Truecaller’s fastest-growing markets.
How It Works
Truecaller operates a crowd-sourced spam identification system. When a user receives a call and marks it as spam or fraud, this information is fed into a database. Machine learning models identify patterns in spam calls:
- Numbers that call repeatedly
- Numbers that spoof legitimate caller IDs
- Numbers that follow geographic or temporal patterns consistent with fraud
- Numbers that use specific scripts or voice characteristics
The system then flags subsequent calls from these numbers, displaying “Likely Spam,” “Suspected Fraud,” or other warnings to users.
Strengths and Impact
Effective Detection: The system is genuinely effective. Truecaller’s data for 2025 showed significant variation in spam intensity across markets, suggesting that the identification system is reliably differentiating spam from legitimate calls.
Accessibility: Truecaller is free, requires no special setup, and works on old and new phones alike. A basic phone user can receive spam warnings with a simple app installation.
Community-Driven Intelligence: The crowd-sourced model is more adaptive than static blacklists. As spammers change tactics, the system adapts based on real user feedback.
Regional Growth: In Africa, rapid adoption suggests that users see real value in spam protection. This demand-pull is important: users are not forced to adopt Truecaller but choose it because it solves a real problem.
Limitations and Privacy Debates
However, Truecaller faces significant limitations and criticism:
Privacy Concerns: Truecaller’s business model requires users to upload their contact lists to enable caller identification. This has raised privacy concerns, with critics arguing that the platform’s data collection practices exceed what is necessary for spam identification.
Network Effects Limitations: Truecaller’s effectiveness increases with adoption. In markets with low adoption, spam identification is less effective. This creates a chicken-and-egg problem in lower-income regions where adoption may be slower.
Regulatory Scrutiny: In Nigeria, the Data Protection Commission has launched investigations into Truecaller’s data processing practices, citing concerns about consent and data minimization.
Not a Comprehensive Solution: Truecaller addresses the symptom (identifying spam) but not the underlying cause (preventing spam calls from being made). With 68 billion spam and fraud calls globally in 2025, even a highly effective identification system leaves room for hundreds of millions of fraudulent calls to reach users.
False Positives: The system is not perfect. Legitimate callers have been flagged as spam, leading to isolation of these callers from their intended contacts.
The Truecaller Paradox
Truecaller’s success has created a curious paradox: the platform is simultaneously evidence of both the scale of the spam problem and the inadequacy of technological solutions. The fact that 500 million people need a spam-blocking app suggests that the underlying infrastructure has failed. The fact that such an app is necessary suggests that regulation and enforcement have been ineffective.
Chapter 10: Telecom Operators Fight Back
Network-Level Interventions
While third-party applications like Truecaller operate at the endpoint (the user’s phone), telecom operators can intervene at the network level, before calls ever reach users.
Airtel’s AI Spam Alert Service: In 2025, Airtel Nigeria deployed an AI-powered spam detection system that scans SMS messages in real-time using over 250 parameters, including sender identity, link structure, message volume, and regional anomalies. Between March 13 and May 20, 2025, the system intercepted 9.6 million suspicious SMS messages.
The system operates at the network layer, automatically flagging suspicious messages with a “Suspected SPAM” prefix before delivery. Each message is processed in less than two milliseconds without storing or analyzing message content, addressing privacy concerns.
The results have been significant: Airtel reported an 84% reduction in spam SMS reaching users in some markets. The system has been deployed across 13 African markets, including Nigeria, Kenya, Zambia, and Uganda.
MTN Network Response: MTN Nigeria, Africa’s largest mobile operator by subscribers, has also invested in spam detection systems. However, specific technical details and results are less publicly disclosed compared to Airtel.
Real-Time Warnings and Blocking: Nigerian telecom operators have implemented systems that warn users in real-time when receiving calls from numbers associated with fraud. Some operators allow users to block entire categories of numbers (premium rate numbers, numbers with spam history, etc.).
Authentication Protocols: Telecom operators have begun implementing STIR/SHAKEN (Secure Telephone Identity Revisited/Signature-based Handling of Asserted Information Using Tokens), an authentication protocol that verifies caller identity and prevents spoofing. However, deployment has been slow due to cost and complexity.
Challenges to Operator Response
Despite these interventions, telecom operators face significant constraints:
Economic Incentives: Telecom operators derive revenue from call volume and SMS processing. Fighting spam reduces call volume. The economic incentive to aggressively combat spam is weaker than the incentive to maximize revenue.
Technical Complexity: Distinguishing spam from legitimate marketing is challenging. A bank’s legitimate SMS alert might appear identical in metadata to a fraudulent phishing message. Operators risk blocking legitimate communications if filters are too aggressive.
International Nature of Spam: Much spam originates outside the operator’s network, entering through international gateways. Blocking international spam requires cooperation with foreign operators, which is often lacking.
Corrupted Infrastructure: Investigations have found that some telecom employees are complicit in fraud. Employees with access to customer databases sell information to fraudsters. Employees with access to network configuration facilitate SIMBox fraud. Internal security is as critical as external security.
Cost of Compliance: Implementing sophisticated fraud detection systems requires significant capital investment and ongoing operational costs. For smaller operators in developing economies, this cost can be prohibitive.
Regulatory Frameworks
The Nigerian Communications Commission has initiated frameworks to mandate anti-spam measures:
- Minimum standards for AI-enabled spam detection
- Real-time reporting obligations for flagged spam
- Periodic audits to verify compliance
- Authentication protocol implementation timelines
However, enforcement remains nascent. Operators that fail to meet standards face fines but rarely face service suspension or license revocation, the ultimate enforcement mechanism.
Chapter 11: Regulations and Enforcement
Comparative Regulatory Approaches
United States: The Telephone Consumer Protection Act (TCPA) and Telecom regulations empower the FCC to enforce rules against spam and unauthorized calls. Individuals can sue for $500-$1,500 per call. However, enforcement is resource-constrained.
Nigeria: The Nigerian Communications Commission, Federal Competition and Consumer Protection Commission, and Nigeria Data Protection Commission all have regulatory authority over aspects of the spam and fraud problem. The FCCPC’s 2025 Digital Lending Regulations are among the world’s most comprehensive. However, enforcement capacity is limited.
Kenya: The Office of the Data Protection Commissioner has been more aggressive in enforcement, issuing significant fines against data brokers and lenders who misuse personal data.
India: The Telecom Regulatory Authority of India has mandated Do Not Call registries and caller ID verification, with mixed results.
Enforcement Challenges
Resource Constraints: A small team of investigators cannot possibly prosecute thousands of daily fraud cases. Prioritization is necessary, but criminals optimize to exploit low-priority cases.
International Jurisdiction: Fraud operators are often located in different countries than victims. Extradition and mutual legal assistance are slow and uncertain.
Speed of Law vs. Speed of Technology: Regulation moves on a 2-5 year cycle. Technology evolves monthly. By the time regulation is implemented, criminals have already shifted to new techniques.
Technical Complexity: Investigating cybercrime requires specialized technical expertise. Many law enforcement agencies lack personnel with these skills.
Corruption: In some cases, corruption within telecom companies or law enforcement enables fraud. Employees selling data, network technicians facilitating SIMBox operations, and law enforcement officials extorting victims create obstacles to enforcement.
What Works (and What Doesn’t)
Effective Approaches:
- Real-time AI-based spam detection at the network level
- Industry cooperation and information sharing between operators and regulators
- Swift license revocation for flagrant violators
- Public awareness campaigns targeting vulnerable populations
- International cooperation and extradition treaties
Ineffective Approaches:
- Static blacklists that lag behind dynamic fraud tactics
- Regulation without enforcement capacity
- Prosecutions that drag on for years
- Fines that do not exceed criminal profits
- Placing all responsibility on consumers to identify fraud
Chapter 12: AI and the Next Generation of Voice Fraud
The AI Inflection Point
The year 2025 represented an inflection point for AI-enabled fraud. The technology crossed from theoretical threat to practical tool, accessible to fraud operators of modest sophistication.
Voice Cloning: AI can now clone a human voice from 3-10 seconds of audio. The cloned voice is indistinguishable from the original for most listeners and for most AI detection systems. The technology is available in dozens of commercial and open-source tools.
Deepfake Video: AI can generate convincing deepfake videos of specific individuals. In early 2024, a Hong Kong engineering firm was defrauded of $25 million when employees believed they were receiving instructions from executives in a video call. The entire meeting was AI-generated—multiple participants, natural interaction, and sophisticated body language.
Large Language Model Integration: Large language models can generate customized fraud scripts, adapt to user responses, and conduct lengthy conversations that maintain internal consistency. An AI system can now conduct an entire fraud operation from initial contact to payment extraction.
Multilingual Operation: AI-generated voices can speak any language. This removes a historical barrier to fraud, the requirement that fraud operators speak the target language. Now a single fraud operation can target speakers of 50+ languages.
The Scale of AI-Enabled Fraud
The statistics are alarming:
- Growth Rate: AI-related fraud attempts surged 194% in 2024 compared to 2023 in the Asia-Pacific region alone.
- Voice Cloning Fraud: Rose 680% in the past year.
- Deepfake Vishing Attacks: Surged 1,633% in Q1 2025 compared to Q4 2024.
- Financial Impact: Global losses from deepfake-enabled fraud reached over $200 million in Q1 2025 alone. Industry projections estimate $40 billion in AI-enabled fraud losses by 2027.
The Psychological Vulnerability
AI-enabled fraud is particularly effective because it exploits human psychology at a fundamental level. When someone hears what sounds like their grandchild’s voice, their rational defenses collapse. When someone sees what appears to be their CEO on a video call, they follow instructions.
One study found that 70% of people surveyed were unsure of their ability to distinguish cloned voices from authentic ones. Human detection accuracy for high-quality deepfake video drops below 30% for many individuals.
The Detection Problem
Traditional fraud detection systems look for inconsistencies: unusual patterns, mismatched metadata, suspicious language. AI-generated fraud minimizes these inconsistencies:
- Voice is consistent in tone, accent, and speech patterns
- Video displays appropriate facial expressions and body language
- Language is grammatically correct and contextually appropriate
- Interaction patterns match expected behavior
The system becomes less about detecting fraud and more about detecting subtle artifacts that indicate synthesis, a problem that improves as AI technology improves.
The Future Trajectory
Industry experts project several concerning developments:
- Fully Automated Fraud: Human fraud operators will be replaced by AI systems that autonomously conduct fraud campaigns from target identification through payment extraction.
- Targeted Deepfakes: Rather than generic deepfakes, fraudsters will create deepfakes targeted to specific victims, using personal details harvested from data breaches and social media.
- Real-Time Adaptation: AI systems will adapt to fraud defense measures in real-time, modifying tactics within seconds of detection.
- Multi-Modal Attack: Coordinated attacks across voice, video, SMS, email, and app-based channels will overwhelm users’ ability to detect inconsistency.
- Synthetic Identity Fraud: Rather than impersonating existing people, AI will create entirely synthetic identities with fabricated histories, employment records, and social media presence. These synthetic identities will be used to establish trust relationships over months before extracting value.
Chapter 13: Market Size of the Fraud-Tec Economy
Global Financial Losses
Reported Losses: Consumer fraud losses in the United States reached $15.9 billion in 2025. Global business fraud losses reached $534 billion in 2025 according to TransUnion.
Estimated True Losses: When accounting for underreporting (2-6.7% of victims report fraud), total losses likely exceed $200-$300 billion globally annually.
Regional Variation: Developing economies like Nigeria likely have proportionally higher fraud impact due to:
- Lower individual incomes (a $500 fraud represents a larger percentage of income)
- Limited financial resilience (no emergency savings)
- Weak law enforcement (lower recovery rates)
Fraud Technology Spending
Companies are investing heavily in fraud prevention:
Defensive Spending: Businesses spent an estimated $50-100 billion globally on fraud detection and prevention systems in 2025. This includes:
- AI-based anomaly detection systems
- Biometric authentication systems
- Blockchain-based identity verification
- Security consulting and investigation services
Offensive Spending: Fraud operators invest in:
- Auto-dialer software and SIP trunk access
- Voice cloning and deepfake technology
- Data broker access and data harvesting tools
- VoIP services and SIMBox hardware
- Social engineering training and script development
The return on investment for fraud is substantially higher than for fraud prevention. A fraudster investing $5,000 in a campaign targeting 10 million numbers expects $200,000-$500,000 in returns. A business investing $1 million in fraud prevention sees value primarily in losses avoided—difficult to quantify and hard to justify to shareholders.
Market Size of Call Identification Companies
Call identification and spam-blocking represent a growing market:
- Truecaller Valuation: The company is valued at approximately $2-3 billion based on market capitalization
- Hiya Valuation: Hiya, another caller ID platform, was valued at $1.5 billion at its last funding round
- Whoscall: Operating across Asia, valued at several hundred million
These companies are profitable or well-funded because the market for spam protection is massive and growing. That market size, billions in annual revenue, reflects the scale of the underlying spam and fraud problem.
Economic Inefficiency
The total economic impact of spam and fraud includes not just direct financial losses but also economic inefficiency:
- Missed Business Opportunities: Legitimate callers unable to reach customers represent lost economic transactions
- Reduced Trust in Voice Communication: When voice calls become untrustworthy, transactions migrate to less efficient channels (video calls, in-person meetings)
- Productivity Loss: Time spent dealing with fraud, filing complaints, and recovering from fraud represents economic loss
- Healthcare Impact: Missed medical appointments and delayed health information lead to higher healthcare costs
- Education Impact: Missed school communications affect student outcomes
The total economic cost of spam and fraud likely exceeds the direct financial losses by a factor of 2-3x.
Chapter 14: Who Profits?
The Ecosystem of Exploitation
Every spam call and fraudulent call represents an extraction of value from victims. This value flows through a complex ecosystem of actors, many of whom are legitimate businesses that profit from fraud without directly committing it.
Fraud Operators: At the center are fraud operators who directly conduct fraud campaigns. They range from solo individuals working from cybercafes in Nigeria, Ghana, or India to organized syndicates operating across multiple countries.
VoIP Providers: Companies providing VoIP services profit from every fraudulent call. A VoIP provider with minimal fraud monitoring effectively subsidizes fraud by providing cheap calling infrastructure. While the provider’s profit per call is tiny, the total profit from millions of calls is substantial.
Data Brokers: Data brokers buy and sell contact lists and personal information. A broker who sells a list of 1 million phone numbers for $1,000 profits regardless of how those numbers are used. Many data brokers know or suspect their customers are fraudsters but maintain plausible deniability.
SIMBox Operators: SIMBox hardware sits in data centers in multiple countries and routes VoIP calls through local SIM cards. The hardware costs a few thousand dollars but can route millions of calls, generating substantial profit.
Call Center Operators: In many cases, fraud operations rent space in shared call centers. The call center operator provides phones, internet, and management but may not directly conduct fraud. They profit from fraud without legal liability.
Telecom Employees: Some telecom employees profit by selling customer data, enabling SIMBox fraud, or pre-registering SIM cards. A single data export can generate thousands of dollars.
Device and Software Developers: Developers creating auto-dialer software, robo-call software, or voice cloning tools profit from these sales, even when intended use is fraudulent.
Financial Services: Money launderers, remittance services, and cryptocurrency exchanges profit from moving fraudulent funds. A money mule moving $10,000 of fraudulent funds takes a 10-30% cut—their profit.
Law Enforcement: In some cases, law enforcement officials extort fraud operators or victims, creating a perverse incentive to continue fraud rather than investigate it.
The Money Trail
Tracking where fraud money goes reveals:
- Initial Extraction: Victim sends money via wire transfer, cryptocurrency, or payment app
- First Layering: Funds move to a money mule or drop account
- Currency Conversion: Funds converted from victim’s currency to another currency (often cryptocurrency) to obscure origin
- Movement Through Multiple Accounts: Funds moved through 3-10 accounts to obscure trail
- Cashing Out: Funds withdrawn at cryptocurrency exchanges, money transfer services, or overseas banks
- Final Destination: Profit distributed among fraud operator, call center operator, data broker, and other ecosystem participants
At each step, a service provider profits. Fewer than 5% of funds are ever recovered, meaning that the money trail is rarely fully traced.
Chapter 15: How Consumers Can Protect Themselves
Individual-Level Protection
While systemic solutions are necessary, individual consumers can reduce their vulnerability:
Caller Identification Tools: Install apps like Truecaller, Hiya, or Whoscall that provide real-time spam identification. No app is perfect, but they reduce exposure to known spam.
Don’t Answer Unknown Numbers: The simplest defense is the strongest. If you don’t recognize the caller, let it go to voicemail. Legitimate callers will leave a message.
Verify Independently: If someone claiming to be from your bank or government agency calls asking for information, hang up and call the organization directly using a number you know. Fraudsters spoof caller ID; they cannot spoof the actual organization.
Never Share Personal Information: Government agencies, banks, and legitimate businesses never call asking for passwords, account numbers, or one-time codes. Never share this information via phone.
Avoid Public WiFi for Financial Transactions: Use mobile data for banking and payments. Public WiFi is vulnerable to man-in-the-middle attacks.
Monitor Accounts Regularly: Check bank and credit card statements weekly. Report suspicious transactions immediately.
Enable Two-Factor Authentication: Use authenticator apps (Google Authenticator, Authy) rather than SMS-based 2FA, which is vulnerable to SIM swap attacks.
Protect Contact Access: Be cautious about which apps you allow to access your contact list. Many apps request this permission but don’t need it.
Enable Phone Spam Filters: Built-in spam filters on modern phones (Google Pixel, Samsung) are increasingly effective.
Community-Level Protection
Report Fraud: File complaints with law enforcement and regulators. Individual complaints create patterns that law enforcement can investigate.
Share Information: Warn family members, friends, and colleagues about fraud tactics. Community awareness reduces vulnerability.
Support Victim Advocacy: Support organizations working on consumer protection and fraud awareness.
Systemic Solutions Required
However, individual protection has limits. When fraud operations are industrialized and occurring at scale, individual behavior cannot protect everyone. Systemic solutions are necessary:
- Regulation of data brokers and data access
- Network-level spam detection mandated for all operators
- Enforcement of consumer protection laws with adequate resources
- International cooperation and extradition
- Technology-based solutions like STIR/SHAKEN deployment
- Prosecution of fraud operators with sentences proportional to losses
- Rehabilitation of corrupted infrastructure
Chapter 16: Future Outlook
Will the Problem Worsen?
Short answer: Yes. Multiple trends suggest that spam and fraud will intensify:
- Improving Technology: AI and deepfake technology will become more accessible and more convincing. By 2027, voice cloning will be indistinguishable from authentic voice for 95% of listeners.
- Increasing Profitability: As fraud losses reach billions annually, investment in fraud infrastructure will increase. Well-capitalized organizations will replace individual fraudsters, leading to more sophisticated operations.
- Expanding Target Base: As more developing world populations gain smartphone access, the target base for fraud expands. Nigeria’s spam intensity is 51%; as connectivity increases, fraud operations will expand to target the remaining population.
- Lagging Regulation: Regulation develops over years; fraud evolves monthly. The gap between regulatory capability and fraudster capability will continue to widen.
- Declining Phone Trust: As phone-based fraud becomes more prevalent, trust in voice communication will continue to erode. This creates economic inefficiency as transactions migrate to less efficient channels.
Can Regulation Catch Up?
Regulation can slow but likely cannot stop the problem. Effective regulation would require:
- International Coordination: Fraud is international; regulation must be coordinated across jurisdictions with shared enforcement mechanisms
- Technology Investment: Regulation must mandate and fund technology-based solutions like STIR/SHAKEN and AI-based spam detection
- Enforcement Capacity: Regulators must be funded adequately to investigate and prosecute fraud
- Speed: Regulatory cycles must accelerate from years to months to keep pace with technological change
This level of coordination is achievable but would require political will and investment beyond what most governments have demonstrated. Nigeria’s 2025 Digital Lending Regulations represent progress but are only a start.
Will Trust in Voice Communication Decline Permanently?
This is the most consequential question. If phone calls become too unreliable for legitimate communication, the consequences extend far beyond fraud:
- Healthcare Delivery: Telemedicine depends on reliable phone communication
- Financial Services: Banking depends on voice communication for customer service and verification
- Government Services: Public health, tax, and emergency services depend on voice communication
- Small Business: Micro and small enterprises depend on voice for customer communication
A world in which phone calls are too unreliable for legitimate use is a world in which connectivity divides widen. Those with access to reliable alternatives (videoconferencing, Internet-based services) will migrate away from voice. Those without access—rural populations, low-income populations, elderly populations—will be left with unreliable phone communication.
The risk is not just fraud but digital exclusion. This outcome is not inevitable but requires preventing through aggressive intervention.
DATA VISUALIZATIONS & RECOMMENDATIONS
Recommended Visualizations
Chart 1 – Spam Intensity by Country (2025) Bar chart showing percentage of unknown calls identified as spam, ranked from Indonesia (79%) to countries with lower rates. Nigeria (51%) clearly visible as Africa’s leader.
Chart 2 – Global Fraud Losses Over Time Line chart showing reported consumer fraud losses from 2020-2025, demonstrating 25-27% year-over-year growth, with projected trajectory to 2027.
Chart 3 – Truecaller Spam Call Detection Volume Stacked area chart showing 68 billion annual spam calls detected by Truecaller, with breakdown by region.
Chart 4 – Deepfake Fraud Growth Line chart showing deepfake-related fraud attempts: 194% growth in Asia-Pacific (2023-2024), 1,633% growth in vishing attacks (Q4 2024 to Q1 2025).
Chart 5 – Data Breach Frequency in Nigeria Bar chart showing 119,000+ data breaches in Q1 2025, compared to prior quarters, demonstrating acceleration.
Chart 6 – Loan App Complaint Categories Pie chart showing breakdown of 11,000+ FCCPC complaints: harassment, data abuse, predatory rates, unethical collection practices.
Chart 7 – Airtel AI Spam Detection Results Bar chart showing 9.6 million suspicious SMS flagged in 2 months, breakdown of on-net vs. off-net sources.
Chart 8 – Spam Call Infrastructure (Flow Diagram) Flowchart showing data sources → contact databases → auto-dialers → spoofed caller ID → victim impact.








